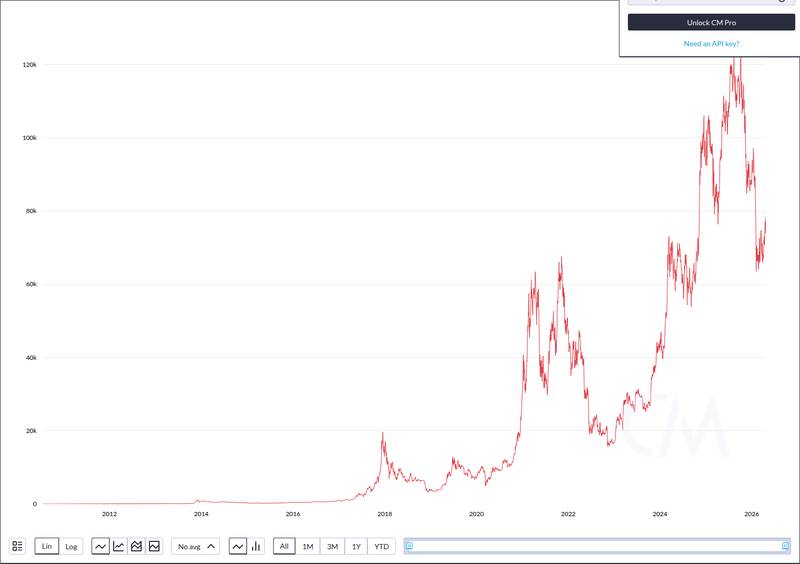
A quantum computing researcher has claimed a 1 Bitcoin bounty after completing what organizers called the “largest quantum attack on elliptic curve cryptography to date,” reigniting debate over whether quantum machines pose a near-term threat to Bitcoin’s security model.
What the 1 Bitcoin Bounty Claim Says Was Achieved
The bounty was awarded by Project Eleven through its “Q-Day Prize” competition. The prize challenged researchers to use a quantum computer to break elliptic curve cryptography, the same family of math that secures Bitcoin transaction signatures.
The winning demonstration targeted a simplified version of the cryptographic key problem. According to Decrypt’s reporting, the researcher broke a simplified key, not a full-strength Bitcoin private key. Production Bitcoin keys are far larger and more complex than the targets used in the demonstration.
The result involved partial proof-of-concept work on a reduced key size. No full private key recovery or signature forgery on a live Bitcoin transaction was demonstrated.
TLDR KEYPOINTS
- Project Eleven awarded 1 BTC for the largest quantum attack on elliptic curve cryptography demonstrated to date.
- The attack targeted a simplified key, not a full-strength Bitcoin private key.
- The gap between this demonstration and a real threat to live Bitcoin funds remains enormous.
Why the Demonstration Matters for Bitcoin Security
Bitcoin relies on elliptic curve digital signature algorithm (ECDSA) cryptography to authorize transactions. When a user spends Bitcoin, their public key is revealed on the blockchain. A sufficiently powerful quantum computer could theoretically derive the private key from that exposed public key.
The risk is most acute for addresses that have already broadcast a public key, either through spending or through older address formats like Pay-to-Public-Key (P2PK). Addresses that have never spent funds keep their public key hidden behind a hash, adding an extra layer of protection.
The technical gap between the Q-Day demonstration and a practical attack on live Bitcoin remains vast. Full Bitcoin keys use 256-bit elliptic curves. The demonstration worked on a dramatically smaller key size, meaning the quantum resources required to scale up would need to increase by orders of magnitude. As regulatory scrutiny intensifies across digital asset markets, the question of cryptographic resilience adds another dimension to Bitcoin’s long-term security profile.
What Remains Unproven After the ‘Largest Quantum Attack’ Claim
The “largest quantum attack” framing describes a record relative to previous attempts, not an absolute capability. Quantum demonstrations in this space typically depend on narrow conditions: small key sizes, ideal error correction, and carefully controlled environments that do not reflect real-world constraints.
Several open questions remain. The hardware scale, qubit count, error rates, and runtime of the winning attempt have not been fully detailed in independent peer-reviewed analysis. Whether the result can be reproduced or extended toward larger key sizes is unclear.
Bitcoin developers have discussed post-quantum signature schemes for years, but no upgrade timeline exists. The demonstration does not change the immediate security posture of the Bitcoin network. No live funds were at risk, and no full-strength key was compromised. Industry participants tracking emerging fintech infrastructure developments will be watching whether quantum-resistant cryptographic upgrades gain urgency.
What the Q-Day Prize does accomplish is establishing a measurable benchmark. Future quantum advances can now be compared against this result, giving the Bitcoin development community a clearer signal for when defensive upgrades become urgent. As legal and regulatory battles reshape crypto market structure, the cryptographic foundations underpinning it all remain, for now, intact.
Disclaimer: This article is for informational purposes only and does not constitute financial or investment advice. Cryptocurrency and digital asset markets carry significant risk. Always do your own research before making decisions.

