
Google has set a 2029 deadline for migrating its authentication services to post-quantum cryptography, a timeline that puts direct pressure on Bitcoin developers still in the earliest stages of upgrading the protocol’s vulnerable signature schemes.
The announcement, published on March 25, 2026, under the title “Quantum frontiers may be closer than they appear,” was authored by Heather Adkins, VP of Security Engineering, and Sophie Schmieg, Senior Staff Cryptography Engineer. Google’s internal target of 2029 is more aggressive than both the NSA’s 2031 target and the US federal government’s 2035 mandate for post-quantum migration.
What Google Actually Said About the 2029 Deadline
Google’s security team warned that quantum computers “will pose a significant threat to current cryptographic standards, and specifically to encryption and digital signatures.” The company framed 2029 not as a cliff but as a preparation window, driven by accelerating progress in quantum hardware, error correction, and factoring resource estimates.
The threat is not purely theoretical. “Store-now-decrypt-later” attacks, where adversaries collect encrypted traffic today to decrypt once quantum computers become operational, make the encryption risk relevant now. Google explicitly recommended that “other engineering teams follow suit” in prioritizing migration.
As part of its own commitments, Google confirmed that Android 17 is integrating post-quantum digital signature protection using ML-DSA, a lattice-based scheme standardized by NIST in 2024. NIST finalized three post-quantum standards that year: ML-KEM, ML-DSA, and SLH-DSA, giving engineers a concrete toolkit for migration.
Why Bitcoin’s Cryptography Is Specifically Vulnerable
Bitcoin uses ECDSA on the secp256k1 curve for legacy transactions and Schnorr signatures for Taproot. Both rely on the elliptic curve discrete logarithm problem, which Shor’s algorithm, running on a sufficiently powerful quantum computer, can solve.
Not all Bitcoin is equally exposed. P2PK outputs, used in early Bitcoin including Satoshi-era coins, expose the public key directly on-chain, making them the most immediately vulnerable. P2PKH and Taproot addresses only reveal the public key when a transaction is broadcast, creating a narrower but still real attack window.
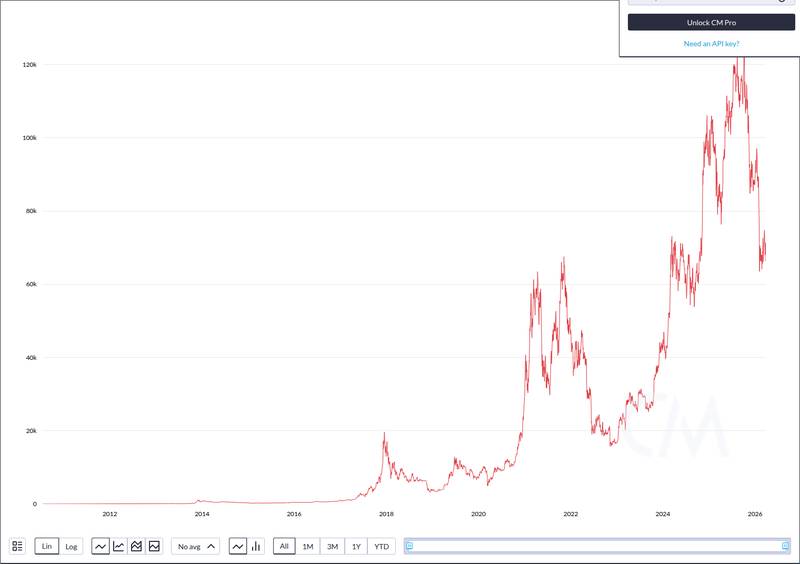
Chaincode Labs estimates that up to 50% of Bitcoin, approximately $700 billion, remains vulnerable to quantum computing threats via attacks on digital signatures. At press time, Bitcoin traded at $66,441 with a market cap of $1.33 trillion.

Current quantum hardware remains far from breaking secp256k1. A cryptographically relevant quantum computer would need roughly 4,000 logical (error-corrected) qubits; today’s best machines operate with hundreds of noisy physical qubits. But Google’s 2029 window suggests the gap is closing faster than many assumed.
The Fear & Greed Index sits at 12, deep in “Extreme Fear” territory, with the quantum threat narrative adding to existing market anxiety. Recent pressure on crypto markets, including sustained ETF outflows on March 27, reflects broader risk-off sentiment.
What a Post-Quantum Bitcoin Upgrade Would Actually Require
BIP 360, which introduces a quantum-resistant address format called Pay-to-Merkle-Root, was recently merged into Bitcoin’s formal improvement repository. It was authored in part by Hunter Beast, who has framed the effort with a clear stance: “Our whole motto is: prepared, not scared.”
But merging a BIP is not the same as activating a protocol change. BIP 360 does not activate anything; it begins the formal process. Any actual upgrade would require a soft fork or hard fork, demanding consensus among miners, node operators, and developers.
Jameson Lopp, co-founder of Casa, has been among the most vocal voices on the challenge. He estimates the protocol upgrade plus migrating user funds could take 5 to 10 years on its own, due to Bitcoin’s decentralized consensus model. If the quantum threat materializes by 2029, Bitcoin may already be running behind.
I’ve been publicly discussing the unique problem of quantum computing risks to Bitcoin for 18 months.
My main takeaway is that I truly hope quantum computing progress stalls and fades away, because adapting BTC to a post-quantum paradigm will be downright nasty for many reasons.
— Jameson Lopp (@lopp) December 21, 2025
Source: @lopp on X
Post-quantum signature schemes also carry a practical cost. ML-DSA signatures are roughly 2 to 3 KB, compared to ECDSA’s approximately 72 bytes. That size increase has direct implications for block space and transaction fees, a nontrivial concern for a network already constrained by its 4 MB block weight limit.
Then there is the UTXO migration problem. Millions of unspent outputs are locked to quantum-vulnerable keys. Coins that never move to quantum-safe addresses would remain exposed indefinitely, raising difficult questions about whether a future soft fork should freeze vulnerable UTXOs, a politically explosive proposition in a community that prizes property rights above all.
The contrast with Ethereum is striking. The Ethereum Foundation has published a four-pronged quantum roadmap targeting 2029 completion and has been running weekly test networks. Bitcoin has a single BIP that does not activate anything and no coordinated roadmap. As broader regulatory and legal scrutiny intensifies across the crypto industry, the absence of a clear quantum defense plan could become a liability.
Bitcoin’s decentralized governance, its greatest strength, may become its greatest vulnerability in a race where coordinated action on a tight timeline is required. Google, a centralized organization, can set a 2029 deadline and execute. Bitcoin cannot. With lawmakers already questioning institutional crypto risk, the pressure to demonstrate preparedness will only grow.
Disclaimer: This article is for informational purposes only and does not constitute financial or investment advice. Cryptocurrency and digital asset markets carry significant risk. Always do your own research before making decisions.

