
A $292 million exploit targeting KelpDAO’s cross-chain bridge has become one of the largest DeFi security failures of 2026, exposing how off-chain infrastructure weaknesses can bypass even correctly functioning smart contracts.
TLDR KEY POINTS
- Attackers drained approximately 116,500 rsETH ($292 million) from KelpDAO’s LayerZero bridge on April 18, 2026.
- The exploit compromised RPC infrastructure feeding data to a single-verifier configuration, not a smart contract bug.
- Aave froze rsETH markets within hours, but pre-hack exposure across its deployments was roughly $1.2 billion.
What the $292M Crypto Hack Means Right Now
Blockchain forensics firm Chainalysis reported that attackers stole approximately 116,500 rsETH from KelpDAO’s LayerZero-based bridge on April 18, 2026. The stolen tokens were worth roughly $292 million at the time of the exploit.
LayerZero confirmed in its official incident statement that the breach was isolated to KelpDAO’s rsETH configuration, which relied on a 1-of-1 Decentralized Verifier Network (DVN) setup. Poisoned downstream RPC infrastructure caused that single DVN to confirm transactions that never actually occurred on-chain.
The scale of the loss is significant relative to KelpDAO’s total footprint. According to Kelp’s Q1 2026 report published just two days before the exploit, the protocol’s total value locked had reached $1.33 billion, and rsETH supply deployed across Aave was approximately $1.2 billion.
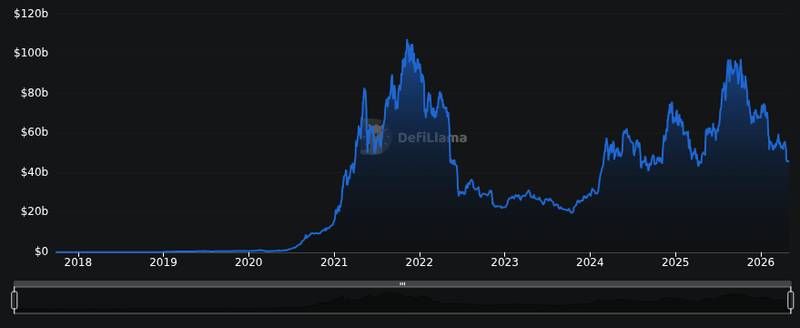
Aave’s Guardian module began freezing rsETH and wrsETH markets across all deployments at 18:52 UTC on April 18, a rapid defensive response given the protocol’s exposure. The broader Ethereum DeFi ecosystem holds over $105 billion in TVL, meaning this single exploit wiped out value equivalent to roughly 0.28% of the chain’s total locked capital.
According to unconfirmed reports, LayerZero and forensic analysts have preliminarily attributed the attack to North Korea’s Lazarus Group or its TraderTraitor subunit, though no independent law enforcement confirmation has been published.
Why the Attack Points to Structural DeFi Security Weaknesses
Off-Chain Infrastructure, Not Code
Unlike most headline DeFi exploits, the KelpDAO breach did not involve a smart contract vulnerability. Chainalysis explained that attackers compromised internal RPC nodes and simultaneously DDoS’d external nodes, feeding false data to KelpDAO’s single verifier. The verifier operated correctly given the data it received; the lie was in the inputs.
Meir Dolev, a security researcher quoted in Decrypt’s coverage, described the attack vector precisely:
“The vault was fine. The guard was honest. The door mechanism worked correctly. The lie was whispered directly to the one party whose word opened the door.”
— Meir Dolev, via Decrypt
Single-Verifier Configuration Risk
The critical design choice was KelpDAO’s use of a 1-of-1 DVN setup. Security researcher Shalev Keren called it “a single point of failure, regardless of what the marketing calls it.” LayerZero’s architecture supports multi-verifier configurations, but KelpDAO opted for minimal redundancy.
This mirrors a pattern familiar to readers tracking incidents like the MANTRA network upgrade, where protocol-level configuration decisions carry outsized security implications. The lesson is consistent: architecture choices made for cost or speed often become attack surfaces.
Audit and Monitoring Gaps
Traditional smart contract audits would not have caught this exploit because the contracts functioned as designed. The failure was operational, sitting in the infrastructure layer between on-chain verification and off-chain data feeds.
The U.S. Treasury’s 2023 DeFi risk assessment had already warned that “poor cybersecurity controls at DeFi services enable theft,” and that DPRK-linked actors actively use DeFi services to transfer and launder illicit proceeds. This exploit fits that official policy framing precisely.
What DeFi Platforms and Users Should Watch Next
Protocol Response Patterns
Aave’s rapid market freeze demonstrated that DeFi protocols can contain contagion when monitoring systems trigger quickly. The freeze began within hours of the exploit, limiting cascading liquidations across the $1.2 billion in rsETH exposure on the platform.
For protocols holding cross-chain assets, the incident has already prompted discussion about mandatory multi-verifier requirements. Projects weighing similar trade-offs between decentralization overhead and security, much like the options market pricing risk after major events, face renewed pressure to prioritize redundancy.
User Risk Indicators
Users re-engaging with bridge-dependent protocols should verify whether the bridge uses multi-verifier configurations, whether RPC infrastructure has undergone operational security audits beyond code review, and whether incident-response playbooks triggered automatically or required manual intervention.
The Fear and Greed Index reading of 39 at the time of writing reflects broader market anxiety. Ethereum traded at $2,308 with a modest 0.38% decline over 24 hours, suggesting the exploit’s price impact remained contained to affected tokens rather than triggering systemic selling.
Regulatory and Trust Implications
If the preliminary Lazarus Group attribution is confirmed, this exploit would represent another data point supporting the regulatory argument for stronger cybersecurity requirements across DeFi infrastructure, a topic also relevant as major crypto platforms navigate compliance pressures.
Visible security improvements, including multi-verifier mandates, real-time anomaly detection, and faster incident containment, will likely determine whether institutional capital continues flowing into DeFi protocols that depend on cross-chain bridges.
Disclaimer: This article is for informational purposes only and does not constitute financial or investment advice. Cryptocurrency and digital asset markets carry significant risk. Always do your own research before making decisions.

